A missing text thread. A deleted file. An employee dispute. A hotel incident that turns into a claim. A family situation where someone is being pressured or tracked. In 2026, the facts you need are often sitting inside a phone, laptop, cloud account, or app log. The problem is that digital evidence is fragile. The wrong “quick fix” can overwrite data, break timelines, or make evidence harder to use later.
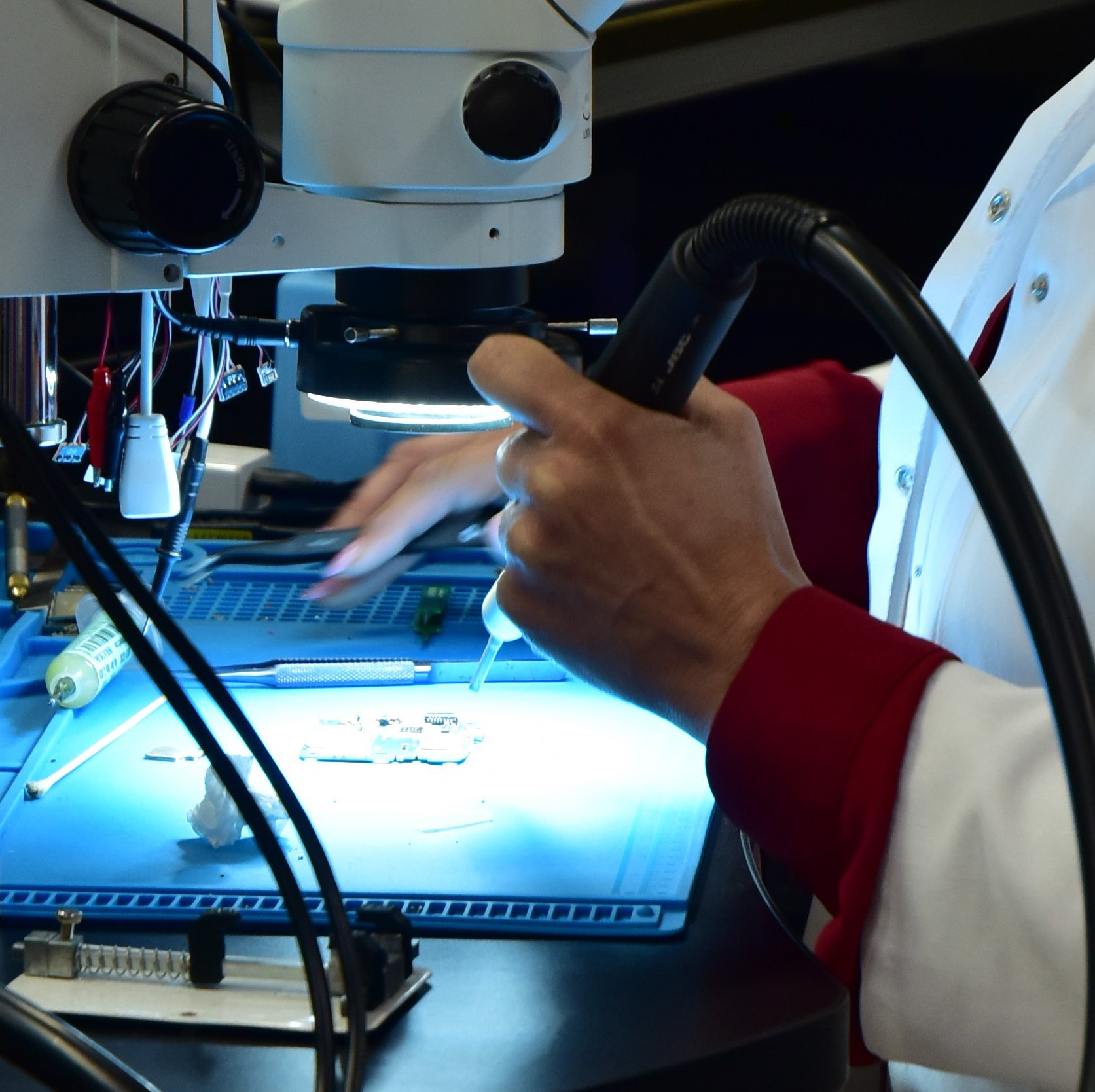
Peralta Associates and Defense support clients across California with cell phone recovery, computer recovery, and professional cyber investigations designed to identify, analyze, and document relevant digital information across devices and platforms using lawful investigative measures.
Why “how you collect it” matters in California
When a case may end up in court, in HR proceedings, or in an insurance investigation, it is not enough to simply find a screenshot. You also need credibility: what was found, where it came from, when it was accessed, and whether anything was altered. In California, the Bureau of Security and Investigative Services (BSIS) licenses and regulates private investigators and private security services, which is one reason businesses and attorneys often prefer a regulated, professional team for evidence handling and reporting.
First steps clients should take to preserve digital evidence
If you think you might need recovery or forensic level review, the best move is to protect the data you already have. Here is what to do immediately.
1) Stop using the device involved
Continued use can overwrite deleted items and change timestamps. If it is a phone, avoid installing apps “to recover data.” If it is a computer, avoid restarts and software updates until you get guidance.
2) Do not “clean up” anything
No deleting messages, no uninstalling apps, no factory resets, no disk cleanup, no wiping “for privacy.” Those steps often destroy the very artifacts that show intent, access, or timing.
3) Document what you see, the right way
Write down dates, times, usernames, device make and model, and what you observed. If you must capture something quickly, take clear photos of the screen and note the time. For businesses and hotels, preserve any related items too, like door access logs, camera export notes, WiFi portal records, and incident reports.
4) Preserve access safely and legally
Only access accounts and devices you own or have clear authorization to access. If an attorney is involved, follow their instructions. If this is a workplace device, keep the chain of custody tight and limit access to a small, designated group.
5) Isolate and secure
Place the device somewhere safe, limit handling, and record who had it and when. This is simple, but it is often the difference between “usable evidence” and “we cannot rely on this.”
How Peralta helps
Peralta’s cell phone recovery and computer recovery services are built for situations where clients need answers without guesswork, plus cyber investigations that focus on lawful, professional documentation that can support legal action, corporate integrity, and private disputes.
That matters whether you are:
- A business owner dealing with internal theft, harassment, fraud, or data leakage
- A hotel or event organizer responding to an incident, extortion attempt, or reputation risk
- A family trying to document harassment, coercion, or custody related communications
- An attorney who needs organized findings and clear reporting
Ready for professional recovery in California
If you suspect important evidence is on a phone or computer, the safest move is to preserve first, then involve a qualified investigative team. Contact Peralta Associates and Defense to discuss cell phone recovery, computer recovery, and cyber investigations and get a professional path forward.